Encryption of data in the Arcium Network is handled at the MXE level. The Arcium Network offers a flexible approach to encryption, allowing Computation Customers to define encryption protocols for each MXE individually. Each MXE operates independently and does not share state with other MXEs. While external solutions can enable encrypted data persistence across multiple MXEs, Arcium does not provide protocol-level state storage. This ensures that every computation remains isolated, preserving confidentiality and security. Arcium’s configurable encryption gives customers the flexibility to customize encryption protocols to suit specific use case requirements. When setting up an MXE, users can choose from a range of encryption options, balancing the need for performance with the level of security. For example,Documentation Index
Fetch the complete documentation index at: https://docs.arcium.com/llms.txt
Use this file to discover all available pages before exploring further.
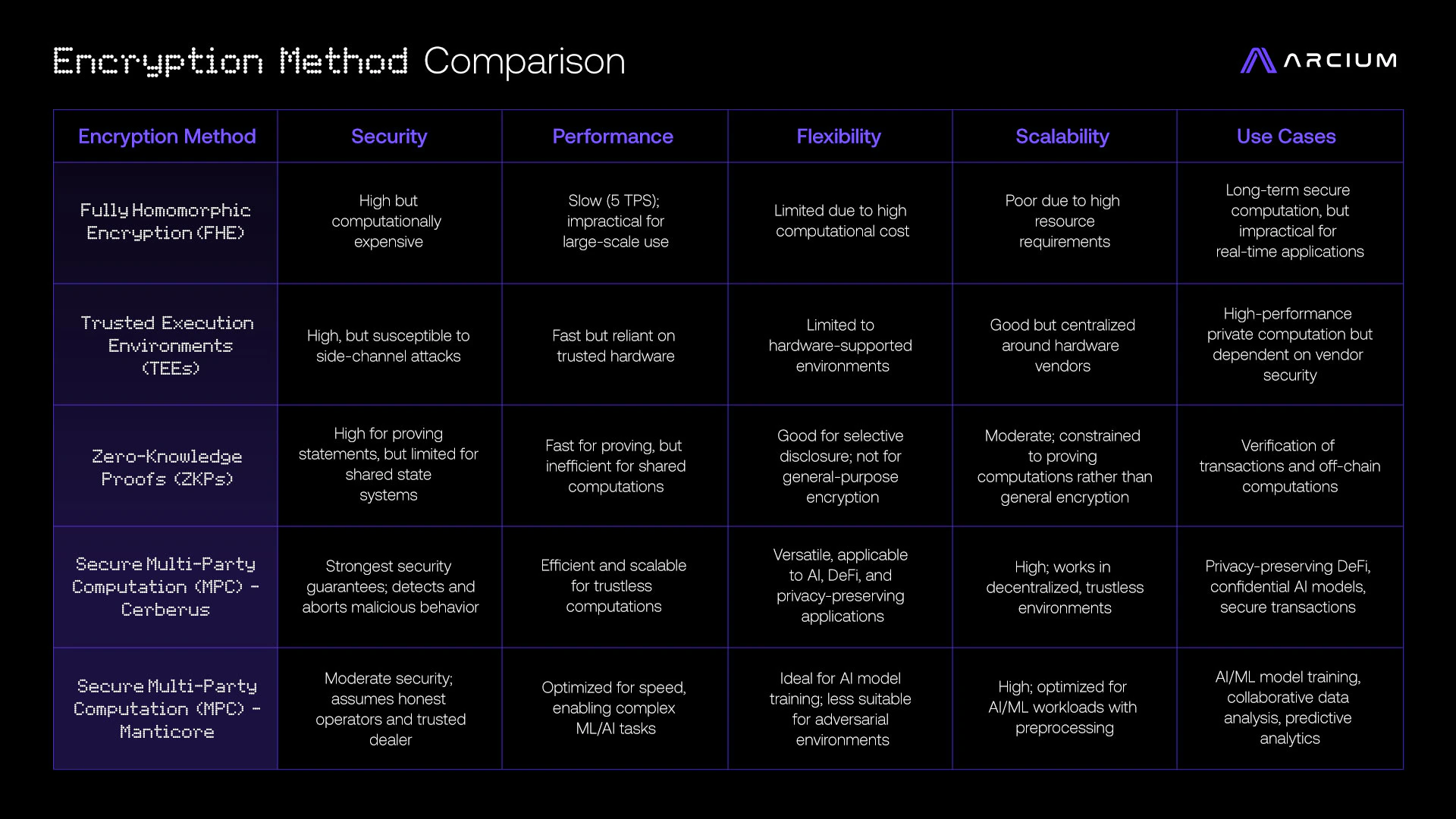
- Lightweight encryption can be selected for tasks prioritizing speed and efficiency.
- Stronger encryption protocols are available for handling highly sensitive data requiring enhanced protection.
Side-channel attack resistance
Some confidential execution platforms, like Trusted Execution Environments (TEEs), rely on hardware to secure data. However, this approach has exposed them to various side-channel attacks (e.g., sgx.fail), making them vulnerable to data leaks and manipulation, which undermines their privacy guarantees. In contrast, Arcium’s Cerberus protocol relies on computational and information-theoretic security, ensuring that even a majority of malicious participants cannot extract or falsify information, provided security assumptions hold. While some MPC implementations can be susceptible to timing attacks—where attackers infer information from slight variations in processing time—Arcium’s solution is to use constant-time operations. This approach ensures that data remains secure, eliminating risks associated with timing-based information extraction.For implementation details on encrypting data in your application, see the Developer Encryption Guide.